by Yiannis Koukouras | Nov 14, 2025 |
There are 3 vectors that define a penetration test engagement. I. Knowledge of the attacker Blackbox The attacker has no previous knowledge of the scope, its technology stack nor the security controls implemented. Graybox The attacker has limited knowledge of the...

by George Roumeliotis | Oct 17, 2025 |
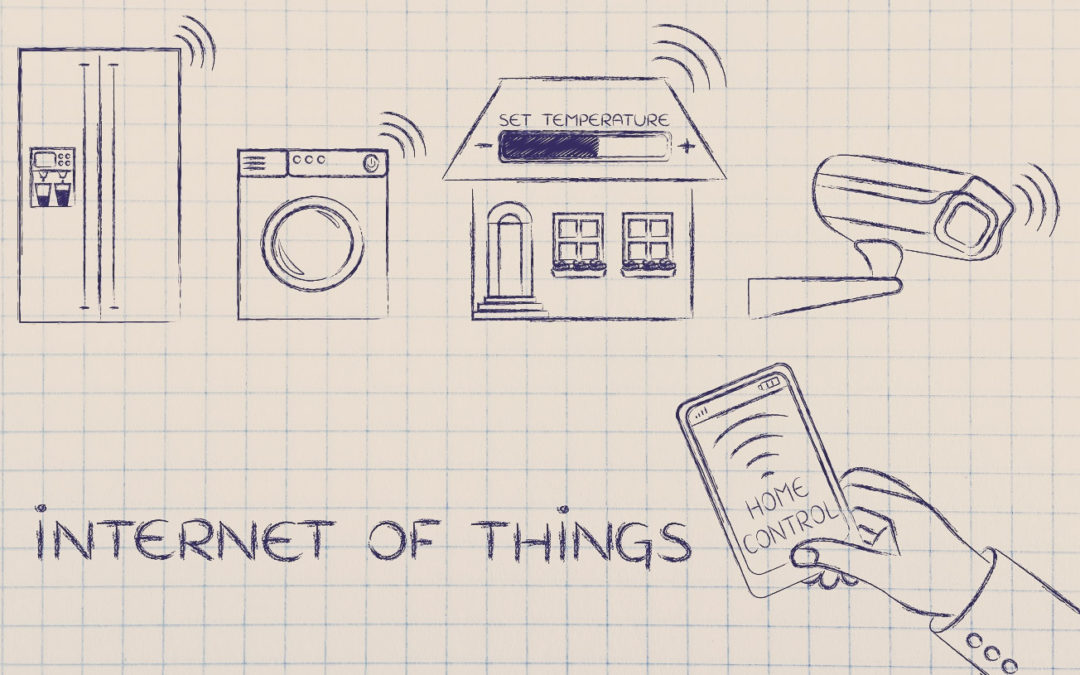
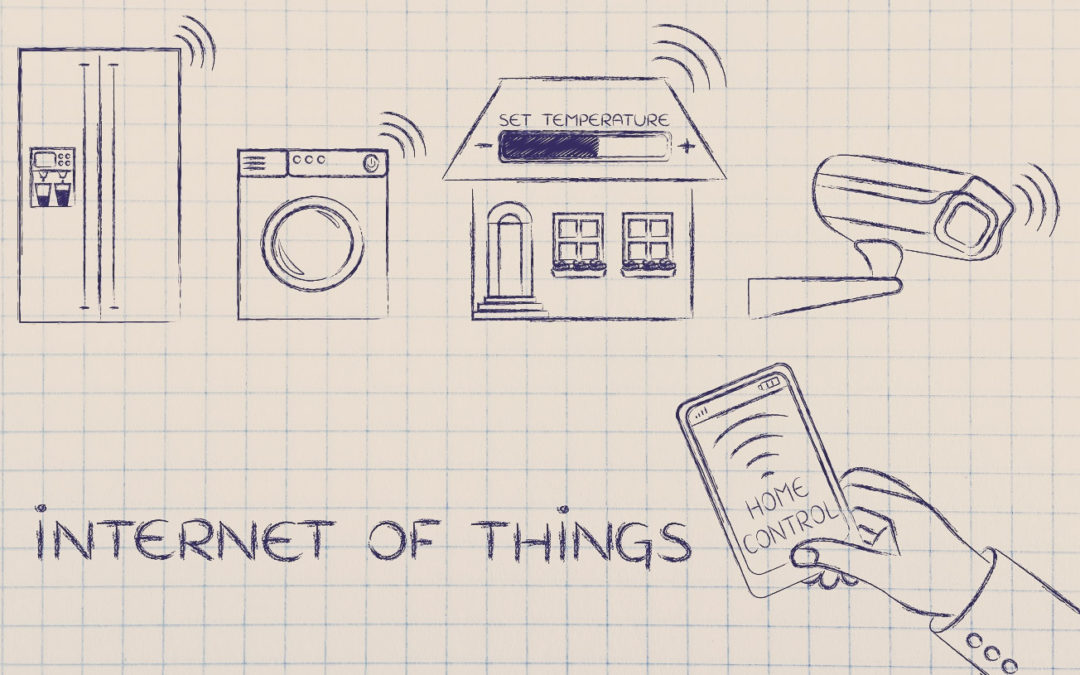
Introduction: The Explosive Rise of IoT and the Hidden Risks From smart homes and medical devices to connected factories and self-driving cars, the Internet of Things (IoT) is no longer futuristic. It’s here, and it’s everywhere. But as the number of...
by Athan Georgopoulos | Feb 5, 2025 |
Intro If you are involved with the infosec community odds are that you have heard the term “red teaming”; but do you know where the term originates from, what does it include when we are talking cybersecurity, and finally is it something that your organisation needs?...
by Aristotelis Koureleas | Jul 24, 2024 |
Introduction In this blog post, we will explore the methods to utilize printers as a means to establish an initial foothold within a network, potentially compromising the domain controller and, consequently, the entire network. We will introduce a newly discovered...
by George Karpouzas | Oct 10, 2018 |
Part 1 In this blog post series, we will show you certain steps among with the tools used in order to conduct IoT security assessments. In this first part you will need a .bin file of a device firmware in order to continue. Tools needed file It...